In the dynamic world of cybersecurity, understanding the nuanced differences between various strategies is key to effective defense – two critical components of a robust security protocol are Vulnerability Assessment and Penetration Testing.
While they are often mentioned in the same breath, they are distinct processes, each with its unique role in fortifying an organization’s cyber defenses.
Vulnerability Assessment: The Diagnostic Phase
Vulnerability Assessment is akin to a thorough health check-up for your organization’s IT infrastructure – it’s a comprehensive process aimed at identifying, quantifying, and prioritizing (or ranking) the vulnerabilities in a system.
Key Characteristics
- Comprehensive Coverage: This assessment scans the entire network, identifying potential vulnerabilities, including outdated software, missing patches, or configuration flaws.
- Automated Tools: It often relies on automated tools to scan systems and networks for known vulnerabilities.
- Regular Exercise: It’s a routine process and should be conducted regularly to ensure ongoing security.
The Outcome
The result is a detailed report listing vulnerabilities, often categorized by their severity, providing organizations with insights into where they are most at risk.
Penetration Testing: The Tactical Drill
Penetration Testing, on the other hand, is more like a fire drill; it’s a simulated cyber attack where professional ethical hackers, using the same tools and techniques as adversaries, attempt to breach your defenses.
Key Characteristics
- Targeted Approach: Unlike the broad scope of vulnerability assessments, penetration tests are typically more focused, targeting specific systems or assets.
- Manual Expertise: It involves a mix of automated and manual techniques, but the expertise of the tester plays a significant role in identifying and exploiting vulnerabilities.
- Scenario-Based: Penetration tests often simulate real-world attack scenarios to understand how systems would fare in an actual cyber attack.
The Outcome
This provides a practical understanding of the organization’s actual defensive capabilities, not just theoretical vulnerabilities.
The Synergy
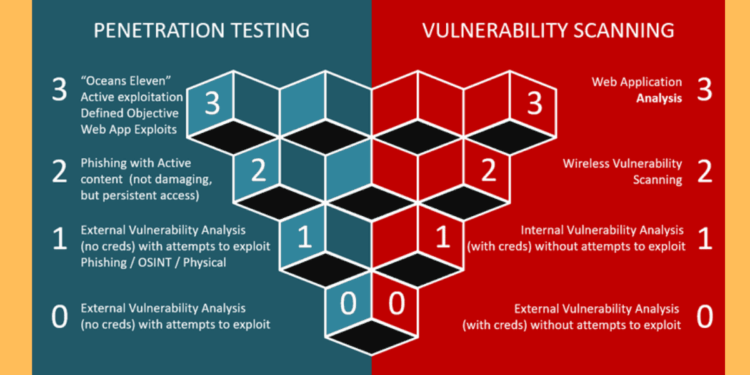
While both processes aim to enhance cybersecurity, they do so in different ways. Vulnerability assessments provide a broad picture of potential weaknesses, whereas penetration tests actively exploit those weaknesses to understand real-world implications.
The Importance of Professional Assistance
Given the complexity and importance of both vulnerability assessments and penetration testing, it’s crucial to have experts you can rely on. Professional penetration testing services not only provide the expertise needed but also offer an outsider’s perspective, which is invaluable in identifying blind spots in your security posture.
In conclusion, while vulnerability assessment and penetration testing are different, they are complementary – an effective cybersecurity strategy will employ both, using the findings from a vulnerability assessment to guide and focus penetration testing efforts. Together, they form a comprehensive approach to identifying and mitigating cyber risks, ensuring that your organization’s defenses are as robust as possible.